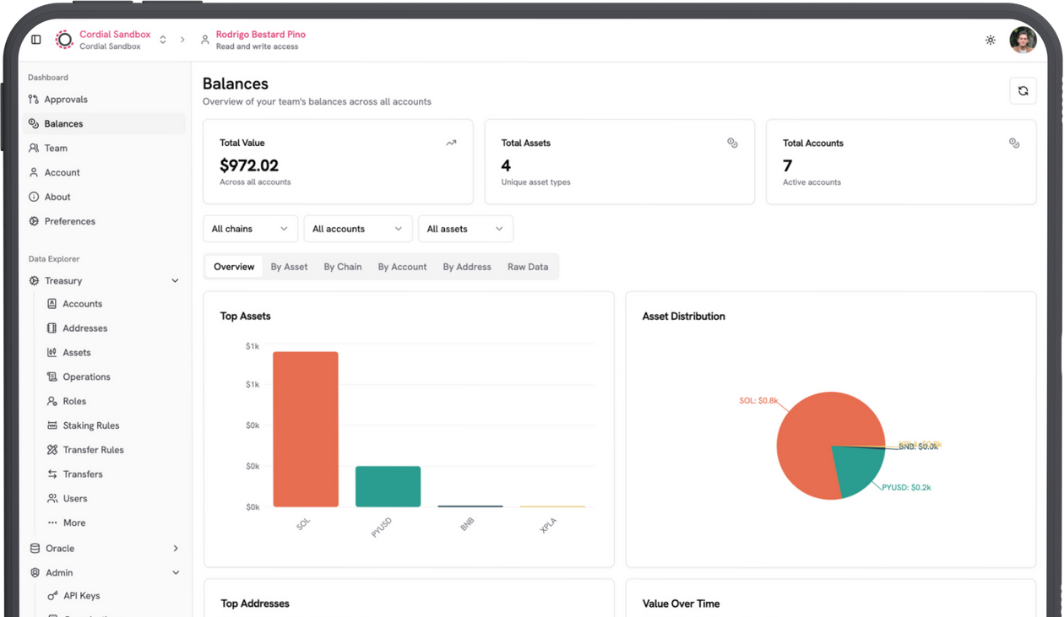
Institutional Crypto and Digital Asset Wallets On Your Terms.
Choose your model. Setup your operating rules. Access all the chains you need.
Your Platform. Your Rules.
Only Cordial Treasury lets you secure and govern your digital assets the way you choose. Run your MPC wallet & governance platform in our secure managed cloud, your private cloud, or fully on-prem.
From "One-click" Setups, to Deeper Integrated Deployments.
Get up and running with the model that makes sense to you, then add your operating rules, and access all the blockchains you need. You can change environments later with zero migration pain.

Are You Asking the Right Questions?
Understand the five pillars of secure, compliant, and resilient custody infrastructure.
Key Share Control
Who controls key generation and distribution: my institution or the vendor?
Policy Governance
Are custody policies defined, enforced, and auditable entirely under my institution’s authority?
Operational Resilience
Can custody operations continue seamlessly if the vendor is compromised or unavailable?
Recovery Autonomy
Can my institution independently restore assets and infrastructure without third-party intervention?
Data Sovereignty
Does the regulator require that servers, IT infrastructure, and sensitive data reside locally within national borders?
Operating Models That You Control
You can simply control the keys and policies, or you can opt-in to running the infrastructure too. Inviting Cordial Systems or trusted partners as additional operators for resilience and redundancy. Choose the responsibility and ownership model that fits your needs today -- and adjust anytime.
Flexible Deployment Models
Cordial makes it easy to choose how your MPC wallet runs. Use our Managed Secure Cloud for the fastest start -- your MPC nodes run inside AWS Nitro Enclaves with hardware-level isolation. When you're ready, move to Co-Hosted or Self-Hosted deployments -- same system, zero migration pain.
Secure Application
Each Cordial node combines a policy engine and a signer, together forming the Secure Application. The signer manages its own MPC key share and communicates with other signers over end-to-end encrypted channels, ensuring keys never leave the network. Every node independently enforces policy before approving operations, this means no single system or admin can act alone.
Enterprise Controls
Cordial's Policy Engine enforces your business rules -- a users permissions, how much of an asset can move, and when. Each node runs its own policy engine. They independently check and then agree on every action before it happens. This distributed approach prevents single points of failure and guarantees byzantine fault tolerance -- essential for institutional security.
Simplified Secure Maintenance
Cordial Treasury handles updates securely and seamlessly. Use our managed cloud or your own infrastructure -- administrators can apply signed updates remotely to keep nodes current. Stay ready for new blockchains, bug fixes, and new features without any operational overhead.
65 Networks. Add New Chains in Days.
Cordial Systems has averaged 2 weeks to add any chain you need and can be as fast as 24 hours. Or, add it yourself with our open source Crosschain library.






Use Cordial's Open-Source Libraries
Integrate New Chains
Your team can independently integrate new chains on your own schedule, without waiting for vendor updates or support queues.
Integrate Exchanges
API key support for centralized exchanges is also built in, enabling capital rebalancing and unified visibility across custody and trading infrastructure.
Complete Operational Flexibility
Maintain complete operational flexibility while expanding asset coverage - on your terms.
Take back control.
Join institutions shifting away from wallet vendors with operational bottlenecks and blackbox products. Reclaim your security, flexibility, and sovereignty with Cordial Treasury.
Send us a message
Book a meeting with a founder
Choose who you want to meet and grab a time that works for you.



















